When a Merkle-Damgård based hash is misused as a message authentication code with construction H(secret ‖ message), and message and the length of secret is known, a length extension attack allows…
Length Extension Attack Baeldung on Computer Science
GitHub - PortSwigger/length-extension-attacks: Length extension attacks in Burp Suite

Workshop 2: Length Extension Attack Zhou Peng March 07, ppt download
Length extension attack. What is length extension?, by Deep RnD
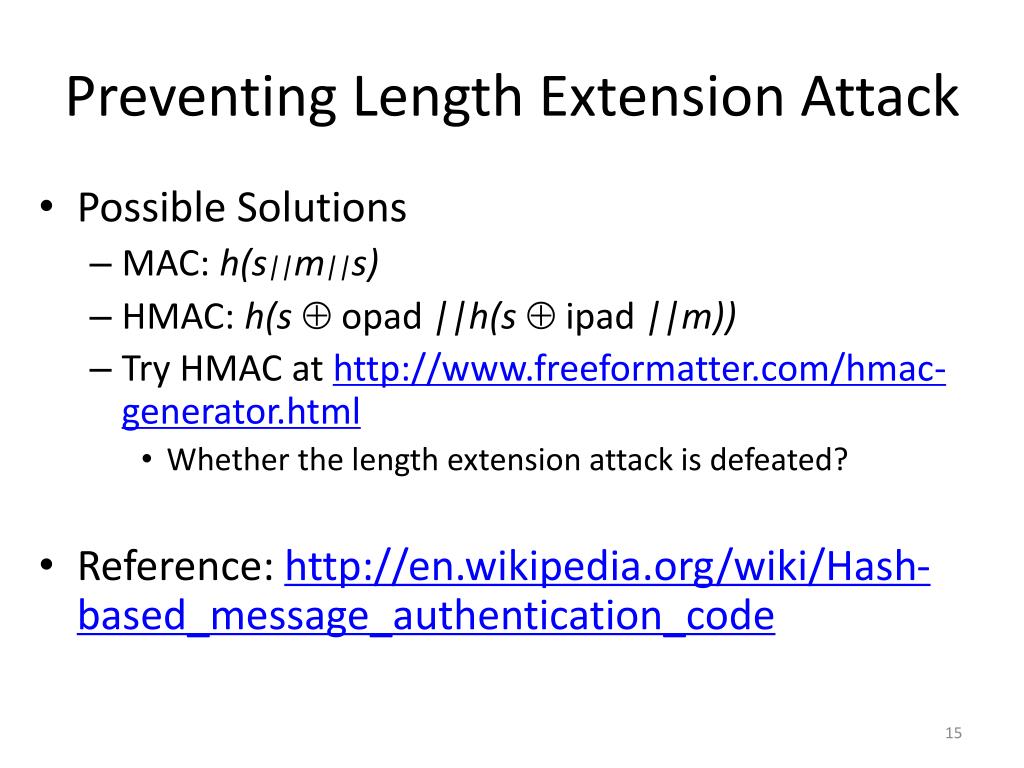
PPT - Workshop 2: Length Extension Attack PowerPoint Presentation, free download - ID:1618604

SOLUTION: Hash length extension attack questions - Studypool
Length extension attack. What is length extension?, by Deep RnD

Mastering Length Extension Attacks: Exploiting Hash Functions

Length Extension Attacks - FasterCapital
GitHub - eid3t1c/Hash_Extender: Automated tool implementing Hash Length Extension Attack in MD4,MD5,SHA1,SHA256,SHA512 along with an example
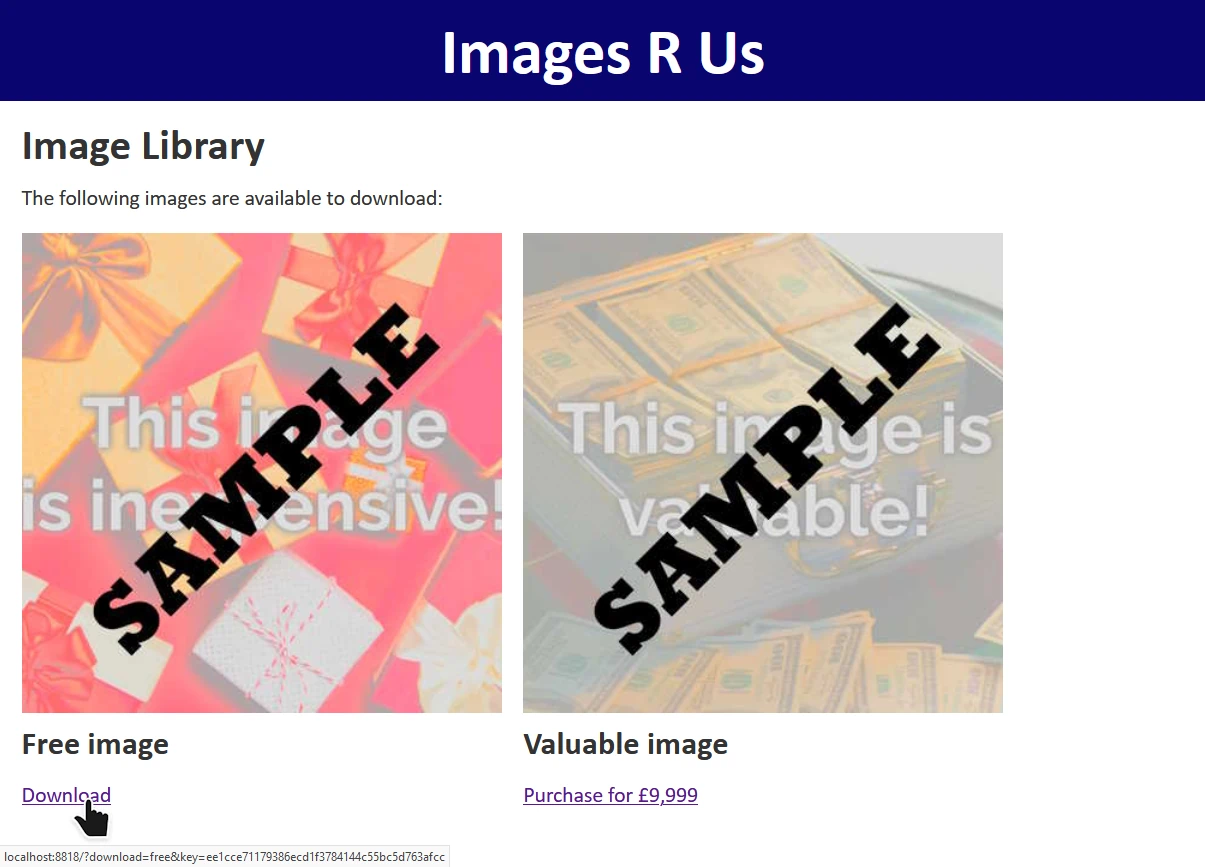
Length Extension Attack Demonstration – Dan Q